Ethical hacking: sniffers In the digital age, cybersecurity is more crucial than ever. Data breaches and cyberattacks continue to make headlines, putting sensitive information at risk and challenging the security infrastructures of organizations worldwide. To counter these threats, ethical hackers—also known as white-hat hackers—employ a suite of tools and techniques to identify vulnerabilities before malicious actors can exploit them. Among the most valuable of these tools are sniffers. In the context of ethical hacking: sniffers, sniffers play a pivotal role in monitoring, analyzing, and securing network traffic.
This article delves into the world of ethical hacking: sniffers, exploring what they are, how they work, their roles in cybersecurity, the risks associated with their misuse, and best practices for using them ethically.
What Are Network Sniffers?
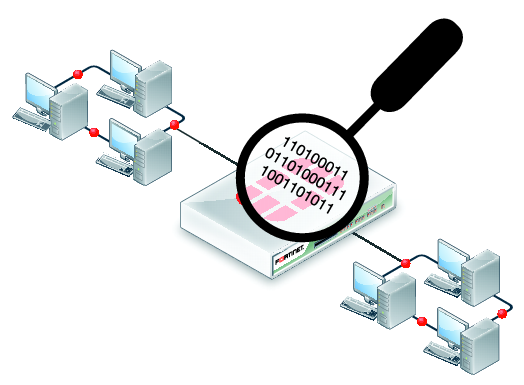
A network sniffer is a piece of software or hardware designed to monitor and capture data packets as they travel across a network. Also known as packet sniffers or protocol analyzers, these tools can capture all data passing through a network interface, allowing the operator to view, analyze, and log network traffic in real time.
Network sniffers can be used for various purposes:
- Monitoring network performance
- Troubleshooting connectivity issues
- Analyzing network usage
- Detecting unauthorized activity or vulnerabilities
- Capturing sensitive information (if misused)
Popular sniffing tools include Wireshark, tcpdump, Cain & Abel, and Ettercap.
How Do Sniffers Work?
To understand the role of sniffers in ethical hacking: sniffers, it’s essential to grasp how they operate. Networks transmit data in the form of packets. Normally, a computer’s network interface card (NIC) only processes packets addressed to it. However, when placed in promiscuous mode, the NIC can capture all packets traveling over the network segment, regardless of their destination.
A sniffer tool leverages this capability to intercept and log network traffic. The captured data can include:
- Source and destination IP addresses
- Port numbers
- Protocols used (HTTP, FTP, SMTP, etc.)
- Unencrypted user credentials
- Sensitive information (like emails, files, or chat messages)
In the hands of an ethical hacker, this information reveals how data moves through the network, highlights potential security weaknesses, and helps identify abnormal or malicious activity.
ethical hacking: sniffers: Why Use Sniffers?
ethical hacking: sniffers is the practice of intentionally probing systems and networks for vulnerabilities, with the permission and knowledge of the owner, to improve security. Sniffers are indispensable in several phases of an ethical hacking engagement:
1. Reconnaissance and Information Gathering
Before launching a simulated attack, ethical hackers use sniffers to map out the network, identify active devices, and determine which protocols are in use. This reconnaissance sets the stage for deeper vulnerability assessments.
2. Vulnerability Assessment
By analyzing captured traffic, ethical hackers can spot weaknesses such as:
- Unencrypted data transmissions
- Weak authentication mechanisms
- Misconfigured services or open ports
- Outdated protocols (like Telnet or FTP)
3. Penetration Testing
Sniffers help ethical hackers test whether sensitive data—such as login credentials or credit card numbers—is transmitted in clear text. If so, they can demonstrate the associated risks to stakeholders and recommend encryption or stronger authentication.
4. Network Troubleshooting and Optimization
Sniffers also assist IT teams in diagnosing network issues, understanding bandwidth usage, and detecting performance bottlenecks.
Sniffers: Ethical Use vs. Malicious Intent
While sniffers are powerful tools for ethical hackers, they can also be exploited by cybercriminals for malicious purposes. Black-hat hackers use sniffers to steal passwords, intercept emails, or eavesdrop on communications—activities that are illegal and unethical.
Ethical hackers follow strict codes of conduct:
- Obtain written permission before using sniffers on any network.
- Limit data collection to the scope of the engagement.
- Safeguard captured data and ensure its secure disposal after analysis.
- Report findings responsibly to the client or organization.
The intent, transparency, and legality of sniffer use are what distinguish ethical hacking: sniffers from cybercrime.
Types of Network Sniffing
There are two primary types of sniffing in network environments:
1. Passive Sniffing
In passive sniffing, the sniffer listens to network traffic without interfering or altering data. This method works best on hub-based networks, where all packets are broadcast to every connected device. Passive sniffing is stealthy and hard to detect.
2. Active Sniffing
Active sniffing involves sending data packets or manipulating network operations to capture traffic—for example, by performing ARP spoofing attacks to redirect traffic through the attacker’s machine. Active sniffing is more detectable but enables sniffing on switched networks, which are more common today.
Ethical hackers may use both techniques—passive for monitoring, active for testing network defenses (with explicit authorization).
Popular Sniffer Tools for ethical hacking: sniffers
- Wireshark: The most widely used open-source network protocol analyzer, offering detailed packet inspection, filtering, and export capabilities.
- tcpdump: A command-line tool for capturing and analyzing network traffic, favored for its speed and flexibility.
- Ettercap: Combines sniffing with man-in-the-middle attack features, useful for testing ARP poisoning and protocol weaknesses.
- Cain & Abel: Known for password recovery and sniffing, though less common in modern environments.
Each tool has its strengths, and the choice depends on the specific goals of a penetration test or security audit.
Risks and Challenges of Using Sniffers
While sniffers are invaluable for security testing, their use comes with challenges and risks:
- Legal and Ethical Concerns: Unauthorized sniffing is illegal and can result in severe penalties.
- Data Privacy: Sniffers can inadvertently capture sensitive personal or business information.
- Detection by Defenders: Modern intrusion detection systems (IDS) and network monitoring tools can spot active sniffing attempts.
- Network Scope: On switched networks, sniffers are less effective unless combined with active techniques.
Organizations must ensure that sniffer deployment is tightly controlled, logged, and monitored—even during authorized tests.
Detecting and Defending Against Sniffers
Defenders can take several measures to detect and mitigate unauthorized sniffing:
- Use Encryption: Protocols like HTTPS, SSH, and VPNs encrypt data, making sniffed packets unreadable.
- Monitor for Promiscuous Mode: Tools like AntiSniff can scan the network for devices in promiscuous mode.
- Implement Network Segmentation: Isolate sensitive segments to reduce exposure.
- Deploy IDS/IPS: Intrusion detection and prevention systems can alert on suspicious activity.
- Regular Audits: Conduct routine security assessments to identify vulnerabilities to sniffing.
Education and strong policies are essential—employees should understand the risks of unencrypted communications and the importance of reporting suspicious devices.
Best Practices for Ethical Hackers Using Sniffers
- Always operate with written authorization.
- Clearly define the engagement scope.
- Minimize data capture to only what’s necessary.
- Securely store and promptly delete collected data.
- Report all findings responsibly and recommend remediation.
- Stay up to date on sniffer tools, network protocols, and emerging threats.
Conclusion
Ethical hacking: sniffers are indispensable tools in the arsenal of cybersecurity professionals. They enable ethical hackers to uncover hidden vulnerabilities, ensure data protection, and strengthen network defenses. However, with great power comes great responsibility—these tools must be used within strict legal and ethical boundaries to protect both organizations and individuals.
As networks grow in complexity and cyber threats evolve, mastering the use of sniffers is essential for any ethical hacker aiming to stay ahead of malicious actors and uphold the security of the digital world.